How Your Camera Becomes a True Random Number Generator
Introduction: The Illusion of Randomness
In classical computing, 'random' is an approximation. Most software relies on Pseudo-Random Number Generators (PRNGs)—sometimes formally called Deterministic Random Bit Generators (DRBGs) in security contexts—that use mathematical formulas to stretch a seed into a sequence. While efficient, these sequences are fundamentally predictable if the initial state is known.
But what if we could anchor our security in the non-deterministic chaos of the physical world? By tapping into the RAW output of a digital image sensor, we can move beyond math and into the realm of True Random Number Generation (TRNG).
In this post, we'll explore how to convert the high-entropy noise from your day-to-day photos into an algorithm for true random number generation. This project resulted in a Python library named photorand, providing a developer-friendly way to harvest true random numbers directly from RAW sensor data.
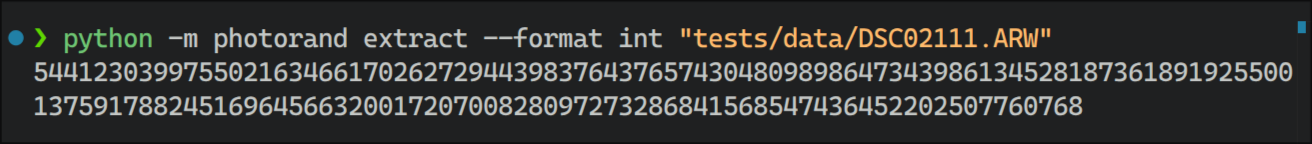
A truly random number, generated from a RAW photo using the photorand CLI utility.
The Physics: The Quantum Noise Floor
Even in a perfectly sealed, pitch-black room, a CMOS or CCD camera sensor is never truly silent. It is a high-precision instrument measuring the chaotic behavior of subatomic particles:
Shot Noise (Quantum Fluctuations): This is the result of the discrete nature of light. Because photons arrive at the sensor following a Poisson distribution, the exact number of hits on a pixel in a given millisecond is a probabilistic quantum event.
Thermal Agitation (Dark Current): At the silicon level, heat causes electrons to transition into the conduction band spontaneously, creating a "shimmer" of electronic noise that is physically impossible to predict.
Read Noise: These are the unpredictable artifacts introduced during the analog-to-digital conversion process.
While a standard camera processor views this noise as an "enemy" to be filtered out, photorand treats it as the ultimate cryptographic resource.
Visualization: Seeing the "Stochastic Delta"
To the human eye, two photos taken a second apart in the same place and conditions look identical. But beneath the surface, your camera is recording a unique, non-repeating "quantum fingerprint" for every single frame.
If we take two consecutive frames and amplify their Least Significant Bits (LSBs)—the tiny increments of data usually ignored by your screen—we reveal the raw noise floor:
Frame A & B (Noise Maps): These grayscale patterns represent the raw electrical signals of the sensor, captured before the camera's internal processing filters out the noise to create a standard JPEG.
The Stochastic Delta (Spectral Heatmap): This image represents the difference between two "identical" frames. Instead of an empty black square, we see a vivid map of unpredictable physical changes, illustrating the raw entropy harvested from the camera's sensor.
Frame A
Frame B
The Stochastic Delta
The Technical Architecture of the photorand Engine
The Extraction Logic: Refining Raw Chaos
This is where we move from physics to the technical algorithm. To turn a messy "rainbow" into secure data, we use a specialized extraction pipeline:
Bypassing the "Digital Interpretation": Standard formats like JPEG use lossy compression that smooths out randomness. We ingest the RAW sensor grid—the "naked" voltage readings—to preserve every bit of entropy.
Surgical Sampling: To ensure the output isn't colored by sensor patterns, we use Grid Stride Sampling, harvesting pixels at fixed intervals (e.g., every 64th pixel) across the entire surface.
The SHA3-512 "Entropy Blender": Raw physical noise can be statistically "biased." We pass the harvested LSB pool through a SHA3-512 cryptographic hash. Due to the Avalanche Effect, changing the state of a single electron on the sensor during exposure results in a completely different 512-bit digest.
Algorithmic Velocity: Scaling with ChaCha20
Extracting high-volume entropy directly from a sensor is computationally expensive. To provide the gigabytes of data required for modern high-speed encryption, we transition from the physical "Root" to an algorithmic "Stream":
The Physical Seed: The 64-byte SHA3-512 digest becomes our "root of trust."
ChaCha20 Expansion Engine: We use the first 32 bytes as a Key and the next 16 as a Nonce. The ChaCha20 cipher then generates an effectively infinite stream of bytes that is computationally indistinguishable from true randomness.
The Protections: This provides Prediction Resistance (adversaries cannot guess future bits) and Backtracking Resistance (if the state is compromised, past outputs remain secure).
Why It Matters
In conclusion, this algorithm provides a physical foundation for true randomness, which has a profound impact on the following fields:
• Unbreakable Cybersecurity: It prevents "entropy starvation"—a state where computers (especially IoT devices) run out of the randomness needed to create secure keys. By using physics, we create encryption that is impossible for hackers to guess or "crack" through patterns.
• Scientific Accuracy: True randomness is essential for "what-if" simulations. It allows researchers to accurately model complex, unpredictable systems like global weather patterns or how new medical treatments interact with the human body.
• Fair Play in Games: It ensures that every digital dice roll, card shuffle, or lottery draw is 100% unbiased. This makes it impossible for players or systems to rig the results, ensuring absolute fairness in digital stakes.
Next time you take a photo, remember: you aren’t just freezing a moment in time. You are capturing the invisible heartbeat of the cosmos—the raw, beautiful chaos of physics that keeps our digital world honest and our secrets safe.